https://abrignoni.blogspot.com/2019/02/android-usagestats-xml-parser.htmlIn this entry I am introducing a parser for the Android recent tasks XML files. Like the previous parser it is based on the research done by Jessica Hyde that she presented at the SANS DFIR Summit 2018. You can see her excellent presentation here:
YouTube: Every Step You Take: Application and Network Usage in AndroidThe presentation slides, in PDF format, can be found here:
PDF Slides: Every Step You Take: Application and Network Usage in AndroidAs explained in the presentation the Recent Tasks XML files record the following activities for recently used apps:
- Task ID number = Used to correlate snapshot and recent image files.
- Effective UID = App identifier.
- First active time = Timestamp in millisecond epoch time.
- Last active time= Timestamp in millisecond epoch time.
- Last time moved = Timestamp in millisecond epoch time.
- Affinity = Bundle ID name.
- Calling package = Bundle ID or process that called the referenced recent task.
- Real activity = Gives information on app usage at time of recording and snapshot creation.
These XML files are located in the following directory:
\system_ce\0\recent_tasks
In addition to these XML files, recent tasks can produce snapshot images as well as recent images. Details about these are contained in the previously referenced presentation. These images can be found in the corresponding directories:
\system_ce\0\shortcut_service\snapshots
\system_ce\0\recent_images
In order to leverage the data contained in these XML files and images I made a parser in Python 3 that takes the XML information and puts it in a SQLite database for ease of querying. The script can be found here:
https://github.com/abrignoni/Android-Recent-Tasks-XML-ParserWarning:
The script has been tested and found to be accurate on my own data sets. Not all recent tasks will contain all data events or related images. Additional testing and validation of the script is humbly requested and more than welcomed.
Script usage
1. Extract from your Android source device the three directories mentioned previously. Extraction should be logical and not contained forensic tool generated recovered items like deleted and/or file slack files.
2. Place the script and the noimage.jpg files from the repository in the same root directory as the extracted directories.
 |
| Have this before running script. |
 |
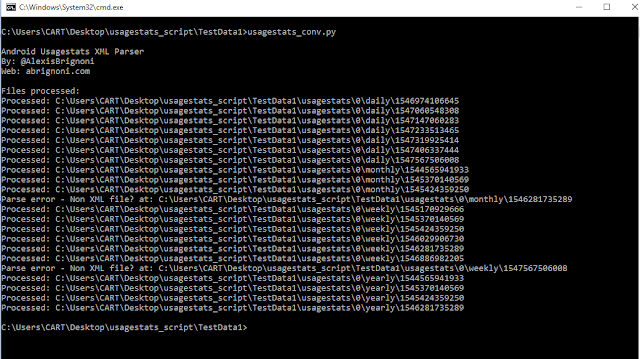
| Script is done. |
 |
| What you should see after a successful run of the script. |
Note that the RecentAct.db SQLite file will contain two fields populated with all the XML attributes in JSON format. The analyst can run a query using JSON_extract to custom generate queries with any of the attributes within the XML.
5. Open the Recent_Activity.html report.
 |
| Sample report entry. |
It is of note that not all recent tasks, in some of my test data samples, had corresponding images or full sets of attributes. When a recent task lacks corresponding images the script will reference the noimg.jp file.
 |
| Missing image and missing attributes. |
Conclusion
I want to thank again Jessica Hyde for her research and for making the community aware of these artifacts. Hopefully this script can make it easier to give much needed context to these images and apps whose value might not be found anywhere else on the source device.
As always I can be reached on twitter @AlexisBrignoni and email 4n6[at]abrignoni[dot]com.